Unsecured Lending via Delegated Underwriting
This document specifies an unsecured lending system that (i) requires no legal recourse, (ii) increases credit limits with repayment, (iii) rewards users for onboarding high-quality new users, and (iv) is Sybil-resistant. It shifts the burden of underwriting from a central algorithm to the edges of the network (the users), incentivizing them to only onboard people they actually trust.
Related work
Our mechanism lies at the intersection of peer monitoring, credit networks, graph-based Sybil resistance, and unsecured lending. The idea of pushing underwriting to the edges of a network goes back to the economics of peer monitoring and joint-liability lending. Stiglitz (1990) shows that when conventional collateral is unavailable, local peers can reduce adverse selection and moral hazard when they bear a localized cost from the defaults of those they back. Our sponsor structure follows this logic: existing users decide whom to onboard, and downstream default harms the path that enabled the loan. Unlike standard joint liability, however, these losses take the form of a bounded reduction in earned credit and delegated capacity rather than open-ended repayment obligations.
The mechanism is also closely related to credit-network models of trust-based finance. Early proposals such as Fugger (2004) treat money and credit as obligations routed through chains of bilateral trust, and later work shows that trust graphs can support liquidity without centralized intermediation (Dandekar et al., 2011; Ramseyer et al., 2020). We adopt this graph-based view of credit, but differ from prior payment-network models in three ways: we study unsecured lending rather than payment routing, restrict trust to a rooted sponsor forest rather than a general graph, and allow successful repayment to generate earned credit that expands future borrowing capacity.
To make such a system viable in a pseudonymous setting, we also draw on the literature on graph-based Sybil resistance and transitive-trust accounting. Yu et al. (2006) show that although an adversary can create arbitrarily many fake identities, the number of attack edges linking the honest region to the Sybil region is limited by the trust extended by honest nodes. Seuken and Parkes (2014) further show that strong forms of transitive trust are difficult to reconcile with Sybil-proof accounting. Our approach is complementary: rather than trying to identify honest users directly, we make delegation credit-conserving, so additional pseudonyms do not create new aggregate lending capacity. They can only redistribute capacity that already enters through trusted seeds or is later created through repayment-generated earned credit. The localized loss rule is also related in spirit to models of financial contagion in networks, where spillovers depend on the capitalization of intermediary nodes rather than on undifferentiated system-wide exposure (Elliott et al., 2014).
Finally, the mechanism can be viewed as a self-contained framework for unsecured lending. It operates entirely pseudonymously, without legal enforcement, upfront collateral, or offchain identity verification. The system uses its internal accounting to manage risk and align user behavior.
Setting
Loans are unsecured with no recovery on default. The system operates in a pseudonymous context, relying on carefully engineered incentives and handpicked seed nodes to achieve low enough default rates.
Goal. Build a system where:
- Borrowers require no pre-existing assets or legal identity, only the trust of a current user.
- Creating multiple fake accounts creates no new borrowing capacity.
- Sponsors (delegators) share in the upside (interest) and the downside (default losses) of their downstream borrowers.
- Credit limits increase with repayments without making strategic default profitable.
The remainder of the document specifies how credit is allocated, how defaults propagate losses, and how interest rates are structured to implement these goals.
Structure
Let \(\mathcal{U}\) be the set of users. A delegation from user \(u\) to user \(v\) is a directed edge \((u \to v)\) with a positive amount \(a_{u \to v}>0\), representing \(u\)'s allocation of \(a_{u \to v}\) units of credit to \(v\). Each user may maintain multiple outgoing delegations.
Seeds are users initialized with a base budget \(\hat{E}_s >0\) and no sponsor. Every other user receives exactly one incoming delegation from their sponsor \(p(v)\), forming a forest of rooted trees.
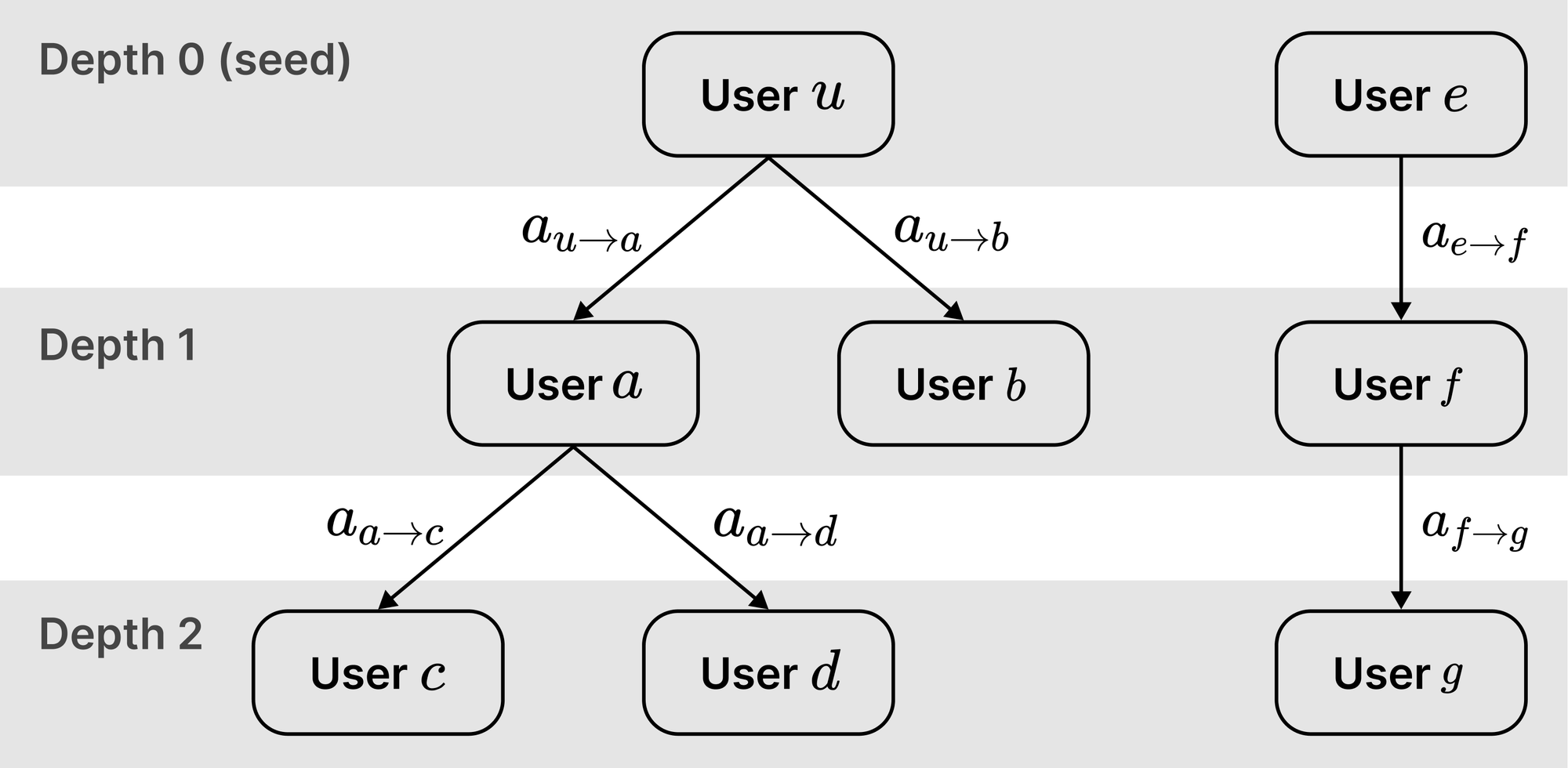
Delegations form paths from a seed \(u_0\) at depth \(0\) to user \(v\) at depth \(d(v)\):
\[u_0 \to u_1 \to u_2 \to \cdots \to u_{d(v)}\quad \text{ where } v=u_{d(v)}\]
Non-seed users can borrow only if an existing user delegates credit to them.
Seed users are manually selected for their ability to repay large amounts and their demonstrated creditworthiness. They are expected to delegate to other high-creditworthiness users through homophily.
Credit allocation
Each user \(u\) has a budget \(E_u\) comprising their incoming delegation (for non-seed users) or base budget (for seed users), plus any earned credit \(G_u\geq 0\) accumulated through on-time repayments.
For a non-seed user:
\[E_u :=a_{p(u)\to u}+ G_u\]
For a seed user \(s\) initialized to base budget \(\hat{E}_s\):
\[E_s :=\hat{E}_s+ G_s\]
User \(u\) has outstanding principal \(x_u\geq 0\) (where \(x_u=0\) means no outstanding loan). At all times, outstanding principal does not exceed the credit limit \(c_u\):
\[c_u := E_u - \sum_{(u\to v)} a_{u\to v}, \quad x_u \leq c_u\]
Equivalently, the protocol enforces \(x_u+\sum_{(u\to v)}a_{u\to v}\leq E_u\) at all times.
Delegation redistributes existing credit rather than creating new credit. When \(u\) delegates \(a_{u \to v}\) to \(v\), \(u\)'s budget remains unchanged while its credit limit decreases by \(a_{u \to v}\). Simultaneously, \(v\)'s budget and credit limit both increase by \(a_{u \to v}\). The system-wide sum of credit limits therefore remains constant.
Total system credit grows only through seed initialization or on-time repayments (which increase \(G_u\)). Small seed budgets constrain tree depth because downstream users lack sufficient credit to support further delegation. Larger seed initialization budgets enable deeper delegation chains and should therefore be sought after.
Revocation
A sponsor \(u\) may reduce delegation \(a_{u\to v}\) only if child \(v\) and its entire subtree remain solvent after the reduction. Solvency requires \(v\) to cover its outstanding principal while maintaining all outgoing delegations at levels that keep descendants solvent.
For each non-seed node \(t\), define the required incoming delegation \(R_t\) as the minimum \(a_{p(t)\to t}\) necessary for subtree solvency:
\[R_t := \max\Bigl\{0,\, x_t + \sum_{(t\to w)} R_w - G_t\Bigr\}\]
Revocation is permitted if and only if the post-revocation delegation \(a_{u\to v}'\) satisfies:
\[a_{u\to v}' \geq R_v\]
This condition guarantees that \(v\)'s credit limit after revocation remains sufficient to cover its own loan and all locked delegations to descendants. If \(v\) then minimizes each outgoing delegation to the minimum-solvent level \(R_w\), its post-revocation credit limit becomes:
\[c_v'=(a'_{u\to v}+G_v)-\sum_{(v\to w)} R_w\]
The constraint \(a'_{u\to v}\geq R_v\) is precisely the minimum needed to maintain solvency.
When \(v\) has no outgoing delegations, \(u\) can revoke down to:
\[a'_{u\to v}\ge\max\{0,\,x_v-G_v\}\]
Sybil resistance
Delegation redistributes credit without creating it. By the definition of \(c_u\), total credit limits equal total budgets minus total delegations:
\[\sum_u c_u =\sum_u E_u - \sum_{(u\to v)} a_{u\to v}\]
Total budgets split between seeds \(\mathcal{S} \subset \mathcal{U}\) and non-seeds:
\[\sum_u E_u=\sum_{v\in\mathcal{S}} E_v+\sum_{w\notin \mathcal{S}} E_w\]
Expanding by budget definitions:
\[\sum_u E_u=\sum_{v\in\mathcal{S}} (\hat{E}_v+G_v)+\sum_{w\notin\mathcal{S}}(a_{p(w)\to w}+G_w)\]
Seeds have no incoming delegations, so total delegations equal all non-seed incoming delegations:
\[\sum_{(u\to v)} a_{u\to v}=\sum_{w\notin\mathcal{S}}a_{p(w)\to w}\]
Substituting into the first equation yields:
\[\sum_u c_u =\sum_{v\in\mathcal{S}} \hat{E}_v+\sum_{u}G_u\]
Total credit limits depend only on seed base budgets and earned credit from repayments. Creating new accounts through delegation does not create capacity; it only redistributes it. A Sybil attacker gains no advantage: every unit delegated to a fake account reduces the sponsor's own credit capacity by that same unit.
Loss propagation
When user \(v\) defaults on principal \(x_v>0\), losses are absorbed first from \(v\)'s earned credit \(G_v\). The absorbed amount and remaining loss are:
\[\delta_v := \min\{G_v,\,x_v\},\qquad \ell := x_v-\delta_v, \qquad G_v \leftarrow G_v-\delta_v\]
The unabsorbed loss \(\ell\) propagates upward from \(v\) to the seed, with each ancestor absorbing what it can from earned credit before passing the remainder higher. After all losses are allocated, the defaulted loan is closed (\(x_v \leftarrow 0\)) and \(v\) loses future borrowing eligibility.
Starting at \(j := v\), iterate while \(\ell>0\) and \(j\) is not a seed. At each step, let \(u:=p(j)\) denote \(j\)'s sponsor and set \(\ell_\text{in} := \ell\). Apply:
- Reduce the delegation: \(a_{u\to j} \leftarrow a_{u\to j}-\ell_\text{in}\)
- Absorb from sponsor's earned credit and update the remaining loss:\[\delta_u := \min\{G_u,\,\ell_\text{in}\},\qquad G_u \leftarrow G_u-\delta_u,\qquad \ell \leftarrow \ell_\text{in}-\delta_u\]
- Move up: \(j \leftarrow u\)
If the loss reaches a seed \(s\) with \(\ell>0\) remaining, the remainder is deducted from the seed's base budget:
\[\hat{E}_s \leftarrow \hat{E}_s-\ell\]
This deduction cannot overdraw the base budget. When the loss reaches the seed \(s\), the amount entering the seed step is the current remaining loss \(\ell\) from its child edge. That amount is bounded by the pre-step delegation on that edge and by the seed’s total budget:
\[\ell_\text{in}\leq a_{s\to j}\leq E_s=\hat{E}_s+G_s\]
Since the algorithm first burns \(\delta_s=\min\{G_s,\,\ell_\text{in}\}\), the residual deducted from \(\hat{E}_s\) is \(\ell=\ell_\text{in}-\delta_s = \max\{0,\, \ell_\text{in}-G_s\}\leq\hat{E}_s\).
Delegations never become negative under this process. Solvency requires \(a_{p(j)\to j}\geq R_j\) for every non-seed \(j\). After absorbing earned credit available in the subtree rooted at \(j\) (including at \(j\)), the remaining loss entering the edge cannot exceed the subtree's required support: \(\ell_\text{in}\leq R_j\leq a_{p(j)\to j}\).
For any intermediate sponsor \(u\) on the path (excluding the defaulting borrower \(v\)), let \(\ell_\text{in}\) be the loss amount that enters the edge \((u\to j)\) to its child \(j\). Immediately, \(a_{u\to j}\) is reduced by \(\ell_\text{in}\) and \(G_u\) is reduced by \(\delta_u=\min\{G_u,\, \ell_\text{in}\}\). If \(\ell_\text{in}>\delta_u\), the remainder \(\ell_\text{out}=\ell_\text{in}-\delta_u\) propagates upward and (in the next iteration) reduces \(u\)’s incoming delegation \(a_{p(u)\to u}\), reducing \(E_u\) by \(\ell_\text{out}\). Therefore the total decrease in \(u\)’s budget is \(\delta_u+\ell_\text{out}=\ell_\text{in}\), matching the decrease in its outgoing delegation on the default path, and \(c_u\) is unchanged overall.
\[c_u'=(E_u-\ell_\text{in})-\Bigl(\sum_{(u\to w)} a_{u\to w}-\ell_\text{in}\Bigr)=c_u\]
For the defaulting borrower \(v\), the budget falls by \(x_v\) while delegations remain fixed, so the credit limit decreases by the principal:
\[c_v'=(E_v-x_v)-\sum_{(v\to w)} a_{v\to w} = c_v-x_v\]
Aggregating across all users, total system credit decreases by the default amount:
\[\sum_{u} c_u' = \sum_{u} c_u - x_v\]
Default causes a permanent reduction in delegation capacity within the affected subtree: the delegations along the seed-to-\(v\) path are reduced by the propagated loss, shrinking downstream users’ budgets. Sponsors also lose earned credit first, and if that is insufficient the loss reduces their incoming delegation (propagating upward).
Interest rates
When a sponsor delegates to \(v\) rather than borrowing directly, they lock their own borrowing capacity. However, if \(v\) defaults, the cash loss is borne by the protocol, while sponsors bear the downside via burned earned credit and reduced delegation budgets/credit limits. To compensate these distinct costs, the borrower pays interest with two components, both due only on full repayment:
- A risk premium \(I^R\geq 0\) compensates the protocol for expected losses when borrowers default. The protocol is assumed to have no other capital costs (e.g., no opportunity cost).
- A delegation premium \(I^D\geq 0\) rewards sponsors on the seed-to-borrower path for locking credit capacity through delegation, even if they contribute no earned credit. This is what incentivizes users to delegate.
On full repayment, total interest is \(I^R+I^D\).
Sponsors are denied the risk premium to ensure they never treat default as an “acceptable cost of business.” If compensated for risk, they could mathematically justify onboarding lower-quality users by offsetting potential losses against gains.
Risk premium
Let \(D_v \in (0,1)\) be the protocol’s estimate of \(v\)’s default probability over the loan term \(T\). Define the risk premium rate \(r^R\) and total risk premium:
\[I^R:=r^R\, x_v \, T\]
With negligible recovery and interest paid only on full repayment, the protocol breaks even when:
\[(1-D_v)\, I^R\geq D_v \,x_v\qquad\Rightarrow\qquad r^R \geq \frac{D_v}{(1-D_v)\, T}\]
This ensures that the expected interest collected from borrowers who repay compensates the expected losses from those who default.
Delegation premium
The delegation premium incentivizes users to delegate and “stake” their credit limit to onboard new users. Deeper delegation paths naturally discourage rent-seeking through higher delegation premium costs.
Define delegation utilization as the fraction of the seeds’ aggregate budget allocated to delegation rather than borrowed or kept as residual borrowing capacity:
\[U^D:=\frac{\sum_{s\in \mathcal{S}}\sum_{(s \to v)} a_{s\to v}}{\sum_{s\in \mathcal{S}} E_s} \in [0,1]\]
The delegation share at the seeds provides a unique manipulation-resistant proxy for overall delegation tightness. The definition is Sybil-robust because \(\sum_{s\in \mathcal{S}} E_s\) is determined by seed base budgets and earned credit, while \(\sum_{(s \to v)} a_{s\to v}\) can only change by reallocating that fixed capacity.
Map \(U^D\) to a delegation-premium rate per unit of locked capacity per unit of time \(r^D(U^D)\geq 0\) using a simple decreasing curve. Let \(r^D_\text{max}>0\) be the maximum delegation-premium rate. Set:
\[r^D(U^D) :=r^D_\text{max}(1-U^D)\]
When \(r^D\) deviates from the target incentive level, users adjust how much they delegate versus how much they keep as borrowing capacity. At the extremes, \(r^D=r^D_\text{max}\) when there is no delegation and \(r^D=0\) when all budget is delegated.
To avoid charging for unused delegation, the delegation premium applies only to the portion of each delegation that is actually locked by this loan.
Let the unique path from the seed to the borrower be:
\[u_0 \to u_1 \to \cdots \to u_d=v\]
Immediately before originating this loan, snapshot all outstanding principals \(x_u\geq 0\) (\(0\) if none) and earned-credit balances \(G_u\). For each non-seed user \(u\), define the earned-credit buffer at node \(u\) (where \(R_w\) is computed from the same origination snapshot):
\[b_u := \max\Bigl\{0,\, G_u - \Bigl(x_u + \sum_{(u\to w)} R_w\Bigr)\Bigr\}\]
Intuitively, \(b_u\) is the portion of \(G_u\) not already needed to support \(u\)’s own loan or other locked subtrees, and is therefore available to absorb additional lockup without increasing upstream required delegation.
Define the incremental upstream-supported notional induced by this loan:
\[z_d := x_v,\qquad z_k := \max\{0,\,z_{k+1}-b_{u_{k+1}}\}\quad \text{for }k=d-1,\dots,0\]
Then \(z_k\) is the additional amount that becomes non-revocable on edge \((u_k\to u_{k+1})\). Next, define the amount of \(u_k\)’s delegation locked by the loan:
\[m_k:= \min\{a_{u_k\to u_{k+1}},\, z_k\}\]
Let \(U^D\) be the delegation utilization snapshot at origination and set the realized delegation-premium rate \(r^D:=r^D(U^D)\). The total delegation premium charged for this loan is:
\[I^D := \sum_{k=0}^{d-1} r^D\,m_k\,T\]
On full repayment, each sponsor \(u_k\) on the path (including the seed \(u_0\)) receives its per-edge delegation payout:
\[\text{delegation payout}\,(u_k) = r^D\,m_k\,T,\quad \text{for }k=0,\dots,d-1\]
These payouts sum exactly to the delegation premium:
\[\sum_{k=0}^{d-1} \text{delegation payout}\,(u_k) = I^D\]
This rule is intentionally local and capacity-based: intermediaries earn even if they contribute no earned credit (\(G_{u_k}=0\)), because they still lock capacity via delegation. Deeper paths generally imply larger total delegation premiums because more edges lock capacity; this discourages unnecessary intermediaries and makes rent-seeking paths expensive rather than profitable.
Earned credit
When user \(v\) repays a loan with principal \(x_v>0\), the protocol grants an earned-credit increment \(\Delta G_v\) that increases their future budget and credit limit:
\[G_v \leftarrow G_v + \Delta G_v\]
To prevent profitable “repay to grow, then default” attacks, \(\Delta G_v\) must not exceed the interest that \(v\) cannot route back to itself, even if it controlled all accounts on the seed-to-\(v\) path. Notably, \(v\) cannot recapture the protocol’s interest, \(I^R\). Earned credit can therefore be safely set to this amount, minted only on full repayment:
\[\Delta G_v := I^R\]
Repaying cannot then increase profit from default, even under worst-case Sybil recapture. If \(v\) repays only to increase budget, then borrows more and defaults, the net gain from “repay then default” versus “default immediately” is at most:
\[\text{profit}\leq \Delta G_v - I^R=0\]
This holds because \(I^R\) is interest that cannot be routed back to \(v\).
Bibliography
Stiglitz, J. E. (1990). “Peer Monitoring and Credit Markets.” The World Bank Economic Review 4(3): 351–366.
Fugger, R. (2004). Money as IOUs in Social Trust Networks and a Proposal for a Decentralized Currency Network Protocol.
Dandekar, P., Goel, A., Govindan, R., and Post, I. (2011). “Liquidity in Credit Networks: A Little Trust Goes a Long Way.” In Proceedings of the 12th ACM Conference on Electronic Commerce, 147–156.
Ramseyer, G., Goel, A., and Mazières, D. (2020). “Liquidity in Credit Networks with Constrained Agents.” In Proceedings of The Web Conference 2020, 345–356.
Yu, H., Kaminsky, M., Gibbons, P. B., and Flaxman, A. (2006). “SybilGuard: Defending Against Sybil Attacks via Social Networks.” In Proceedings of the ACM SIGCOMM Conference, 267–278.
Seuken, S. and Parkes, D. C. (2014). “Sybil-proof Accounting Mechanisms with Transitive Trust.” In Proceedings of the 13th International Conference on Autonomous Agents and Multiagent Systems (AAMAS).
Elliott, M., Golub, B., and Jackson, M. O. (2014). “Financial Networks and Contagion.” American Economic Review 104(10): 3115–3153.

